Where did you get your intel from? :)
If I'm reading this article on The Register correctly, it seems anyone with an Intel-powered computer can look forward to a loss of performance in the near future. On the other hand, if you're an AMD user, you can feel pleased with yourself. Sadly, I'm all Intel-ed up at the moment. :-(
Where did you get your intel from? :)
Got a new watch, divers watch it is, had to drown the bastard to get it!
Indeed, this looks like a huge win for AMD's Ryzen.
This has the potential to very seriously upset a great many people. Class action against Intel?
Last edited by markrlondon; 3rd January 2018 at 19:54.
I suspect it's a very deep and quite old bug, but Intel are saying nothing rather than give hackers more info than they need. There's no sign yet that it's been taken advantage of.
Seeing this breaking on BBC news a couple of hours ago bought the memories flooding back ....
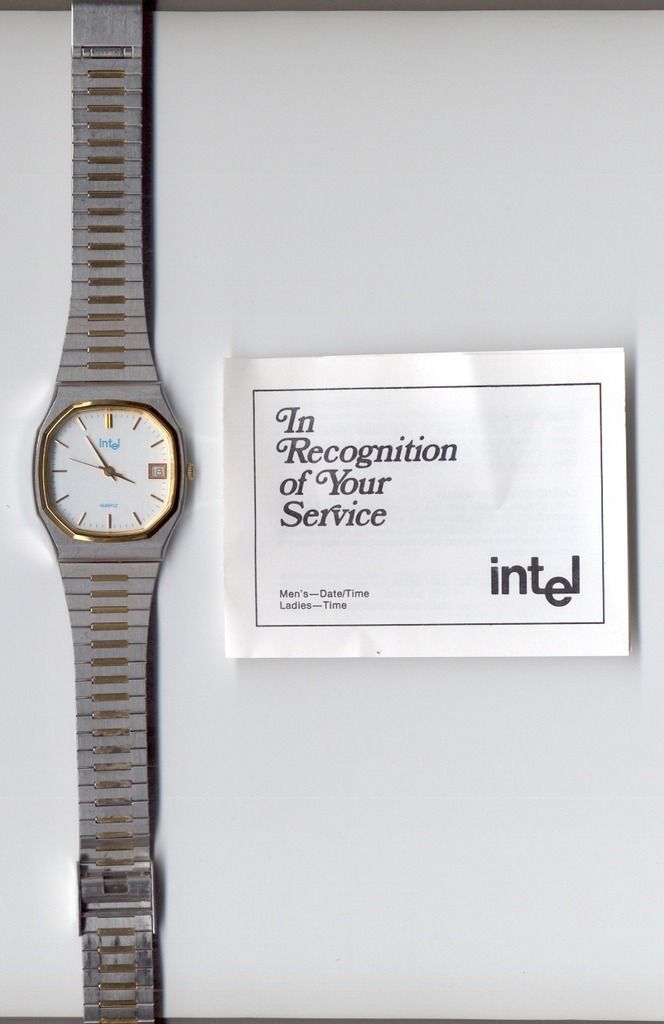
I was working for Intel (as Senior Logistics Planner in their European Product Service Operation) back in 1994 - when the P5/P54 (Pentium I 60Mhz / 66Mhz) Floating Point Bug error went public.
https://en.wikipedia.org/wiki/Pentium_FDIV_bug.
Interesting times indeed !
http://www.columbia.edu/~sss31/rainb...ium.jokes.html
Q. What do you do with tens of thousands of unsaleable wafers ?
A. Give them away as marketing freebees, embedded in keyrings, paperweights and cheap quartz watches !
I still have a few other souvenirs (My 5 year service award watch was presented to me by CEO Andy Grove).
It's not the fact that it (probably) hasn't been exploited yet that is the issue; it's that people's computers look likely to be seriously slowed down on certain types of task.
Depending on the slow down, this could be a huge problem. In the UK and EU I think it would justify people asking for their money back (or cash compensation) from retailers under consumer protection legislation.
The important question is: can americans sue Intel for millions of dollars ?
I don't claim to be a kernel programmer but on Linux this appears to be the case. The first code to fix the bug was targeted at all all x86 processors but AMD provided a patch that exempts their CPUs being affected by the code.
Hopefully Microsoft have provided similar discrimination between Intel and AMD CPUs in their Windows fixes but this is not yet known.
Last edited by markrlondon; 4th January 2018 at 16:04.
Latest news summary here: Meltdown, Spectre: The password theft bugs at the heart of Intel CPUs https://www.theregister.co.uk/2018/0...vulnerability/
And it's actually worse than it seemed.
Last edited by markrlondon; 4th January 2018 at 16:10.
More from the BBC:
Intel, ARM and AMD chip scare: What you need to know
Nearly all computers worldwide - and many other devices - have been exposed to security flaws which leave them vulnerable to attacks by hackers.
Researchers discovered gaps in security stemming from central processing units - better known as the chip or microchip - which could allow privately stored data in computers and networks to be hacked.
So far no data breaches have been reported. So is it a big deal and what does it mean for you?
...
Rush to fix 'serious' computer chip flaws
Tech firms are working to fix two major bugs in computer chips that could allow hackers to steal sensitive data.
The bugs are an "absolute disaster" and need to be fixed promptly, according to one cyber-security researcher.
Google researchers said one of the "serious security flaws", dubbed "Spectre", was found in chips made by Intel, AMD and ARM.
The other, known as "Meltdown" affects Intel-made chips.
...
So, not only intel then?
Got a new watch, divers watch it is, had to drown the bastard to get it!
The latest macOS, version 10.13.2 is safe from the meltdown bug so mac users update if you haven't already.
The most egregious and immediate problem (which is called 'Meltdown') is all Intel (and a few ARM processors). Meltdown cannot be patched with CPU microcode; it needs operating system fixes (which are the ones that slow systems down) and physical design changes in CPUs.
The other problem ('Spectre') affects Intel, AMD and ARM but is less serious in some ways in that it is harder to exploit. Happily it can probably be fixed in CPU microcode but these patches are not yet available.
Overall, Intel's CPUs are definitely the main problem as things stand right now. Intel CPUs and computers with Intel CPUs on sale right now, today, contain the Meltdown bug.
If you're buying a desktop, laptop or server computer today (and for the foreseeable future) you should choose one based upon an AMD processor (such as Ryzen). This will still suffer from the Spectre bug (until a microcode fix is released for it) but you won't suffer the possible slowdown due to the Meltdown bug that only Intel (and a few ARMs) suffer from.
Check out the summary section of Meltdown, Spectre: The password theft bugs at the heart of Intel CPUs. Search for "Here's a summary of the two branded bugs" to see the summaries.
Last edited by markrlondon; 4th January 2018 at 16:57.
Daily update checks for my W10 laptop.
And I just found one...but it's KB4056892 and not the fix for the security flaws.

Apologies if seems silly 😜 question but will this affect my I pad ?
That's the one. It's totally not clear from the description but apparently it contains the fix for Meltdown.
P.S. Well, that's what is claimed by a Microsoft representative here: https://answers.microsoft.com/en-us/...0-ddbca40b9ac1
But when I go to the Security Update Guide and search for "CVE-2017-5754" (which the vulnerability code for Meltdown) there's no hit! (For reference, CVE-2017-5753 and CVE-2017-5715 are the codes for Spectre).
So either KB4056892 is not the patch that contains the Meltdown fix or Microsoft have not listed the vulnerability properly.
P.P.S. I found this security advisory, ADV180002 | Guidance to mitigate speculative execution side-channel vulnerabilities, from Microsoft which is useful and appears to confirm that KB4056892 (i.e. January 3, 2018 updates) is the correct fix for Windows 10.
The ADV180002 advisory links to KB4073119 Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities which has further VERY useful information, including a method of confirming whether or not the patch for both Meldown and Spectre is installed.
In fact here is the relevant diagnostic information:
Verifying protections are enabled
To help customers confirm whether protections have been enabled, Microsoft has published a PowerShell script customers can run on their systems.
Customers can install and run the script by running the following commands:
The output of this PowerShell script will look like the following. Enabled protections will show in the output as “True”.PowerShell Verification
Install the PowerShell module
PS > Install-Module SpeculationControl
Run the PowerShell module to validate protections are enabled
PS > Get-SpeculationControlSettings
PS C:\> Get-SpeculationControlSettings
Speculation control settings for CVE-2017-5715 [branch target injection]
Hardware support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is present: True
Windows OS support for branch target injection mitigation is enabled: True
Speculation control settings for CVE-2017-5754 [rogue data cache load]
Hardware requires kernel VA shadowing: True
Windows OS support for kernel VA shadow is present: True
Windows OS support for kernel VA shadow is enabled: True
Windows OS support for PCID optimization is enabled: True
P.P.P.S. Remember to look for BIOS updates for your laptop, desktop or server, as these will contain CPU microcode updates that might be needed as well as the operating system patches in Windows, Linux, etc.
Last edited by markrlondon; 4th January 2018 at 17:40.

Interestingly, I haven't seen anything from Apple yet and they weren't on the original notification list (oops!). Apple use a modified Arm SoC in iDevices and some Arm cores are confirmed vulnerable, so it seems extremely likely that most Apple cores (no pun intended) will be as well as they are using the same CPU architecture (albeit to their own specs).
For the non-technical, Arm don't really make CPUs like Intel and AMD do. They design and licence various aspects of them, which Apple are using. They call it an Apple processor and do design some bits in-house. An Android device will most likely be called Arm Cortex or something. They are mostly made by the same companies (Samsung and TSMC).
There's a useful summary of advisories, patches and updates here: List of Meltdown and Spectre Vulnerability Advisories, Patches, & Updates
It confirms that KB4056892 is the patch for Windows 10. If only Microsoft's own tools made this clear!
Re "Verifying protections are enabled" at #20 above.
I'm managed to open a Powershell widow...as an administrator (see link)...but none of the commands (as written on the MS page) seem to work. Specifically, it returns that Install and Get are not recognised as the name of a cmdlet.
Any advice / suggestions will be gratefully received.
(Bold added by me)
The commands are as follows:
In other words, "Install-Module" has a dash linking the two words that make up the command (followed by a space and then "SpeculationControl").Code:Install-Module SpeculationControl Get-SpeculationControlSettings
Similarly "Get-SpeculationControlSettings" has a dash linking the two words that make up the command.
^^^^^^^
Progress...I think.
"Install-Module SpeculationControl" now returns a window asking "How do you want to open this file?" Once again...any suggestions, please?

That took some doing...!
First I had to install Visual Studio Community 2017 from this link (plain install...none of the offered options needed).
That got the module to install.
Then I had to use 'Set-ExecutionPolicy RemoteSigned' before 'Get-SpeculationControlSettings' to let it run.
I also tried 'Set-PSRepository PSGallery' as I was warned that the source for the module was not trusted...but I'm not sure if that did anything...

Cheers for the info Mark, Im making sure my devices have this patched up.
I dont like to be too paranoid about cyber security, but this looks like a bit of a doozy.
Im assuming fenced-in ecosystems like iOS are more robust against attacks exploiting this flaw ie clicking on a webpage in Safari cant let malware in?

Not at all. It is an absolute doozy b/c the Spectre issue affects the fundamental design of ALL processors. The flaw shown by Spectre will require a complete re-architecture of the way processors are designed and the threats posed will be with us for an entire hardware lifecycle, likely the next decade. Patching works for now to halt the 'Meltdown' flaw but the wider issue is huge for Intel, ARM, AMD.

No, the proof-of-concept works with JavaScript running in a browser, so it would only take a visit to a malicious website, or a website that pulls in ad/tracking data from elsewhere and that is compromised (this has happened in the past on supposedly legitimate ad networks so it's not far-fetched). An exploit that actually installs malware this way isn't impossible, but it's much more difficult than one that simply steals private data, though obviously that's bad enough as it is.
I would say the chance of an exploit in the wild right now is relatively low because this was found by security researchers first, so the fixes should be out before the exploits start happening. It's also quite CPU-intensive to exploit in the first place, making it easily detectable before an attack would be successful (i.e., you'd probably notice the webpage was really slow and press back or close the browser). So for that reason the risk is reasonably low for home computers, but it's not something anyone running a server can ignore, especially if they deal with sensitive data of any kind. Those will be the first targets. And of course you definitely want to install the OS and firmware patches for this as soon as they are available.

Ta. As as non-techie civilian, its often quite difficult to gauge the risk of this kind of thing. I generally assume that when something gets in the papers, its a fairly major balls-up, but even then the press can exaggerate the real world risk. On the other hand, identity fraud is a pain in the arse I can do without, after knowing a few people whove had it done.

Oh, as far as the IT world is concerned this is the equivalent of World War 3 breaking out, no mistake about that. This is probably be the biggest security flaw ever found since Alan Turing broke the Enigma machine.
However, for the average user we're not quite into Mad Max territory just yet. It's really just business as usual as far as the typical security advice goes: keep your system patched up to date and beware of suspicious emails, dodgy websites, etc. The only difference is that if a patch comes out over the next couple of weeks, you should apply it NOW. Not tomorrow, not the day after, NOW. It's only a matter of time before exploits start appearing in the wild.
What is going to be interesting is all the devices that are vulnerable but for some reason can't be updated, which I think will be surprisingly many because of the disposable culture that's developed around software over the last 5-10 years.
For example Apple has already dropped support for a lot of "older" hardware in the latest versions of iOS, but much of that hardware may still be vulnerable. It remains to be seen how far back they are going to patch those systems, although with previous major serious security issues they have been pretty good about that.
For Android devices it's much worse, because unless you have a Google Nexus you probably have close to zero software support from the manufacturer and most likely won't receive any OS patches even after Google releases them. It's all that stuff that's going to turn into a complete nightmare in the coming months as exploit kits start becoming widely available and attention starts to move away from servers, which will almost all have been properly secured by then, to all those unsecured devices in the hands of average users.

It's worth considering switching on site isolation in browsers to stop sites stealing cookie data from other sites. Chrome is https://support.google.com/chrome/an...23121?hl=en-GB but it does come with a 15-20% memory increase hit. Firefox also has it built in for latest version but you need to switch it on. See https://www.ghacks.net/2017/11/22/ho...on-in-firefox/
FF has also updated to add other mitigations see https://blog.mozilla.org/security/20...timing-attack/
Note site isolation may interfer with authentification on some sites.
The other option is use separate browsers and keep important things like banking to a single browser that you can clear caches etc from. Do other internet stuff from another.

As with all these newly announced vulns, many consumers will worry unnecessarily while still using their unsupported Windows XP machines and unpatched OSes with hundreds of exploitable vulnerabilities.
Make sure you use supported software and install all vendor patches when they are published. Where you cant, and in a corporate environment, introduce mitigating controls.
Fix the 1000 day vulns before you worry too much about this weeks.
Last edited by slever; 5th January 2018 at 21:26.

Relatively understandable explanation from Apple here:
https://support.apple.com/en-us/HT208394

What I don't really follow is why this is such a big deal, from what I have read (and I could be wrong) these can only be exploited by having code running on your cpu. So it seems to me that this is a virus like situation, the possibility is there but you need to have an 'infected' piece of code running to exploit it.
Or am I wrong?
If you use Linux distro would the problem be as bad? I know the CPU is the problem, but Linux has more inbuilt safety features in it doesn't it?
Agreed.
This, absolutely this. There are going to be millions of unpatched and unpatchable devices in use for many years to come. Mostly, as you say, they'll be mobile phones (primarily Android) but many will also be desktop and laptop PCs (and even some smaller servers) either running older Windows or un-updated Linux or where the hardware manufacturer no longer produces BIOS updates[1]. Additionally, a great many IoT devices seem unlikely to get updates (although this may in theory matter less since such devices rarely run arbitrary code).
All in all, this is potentially a paradigm-changing event, although the exact fall out is yet to be determined. I know that I won't be buying Intel CPUs or Intel stock any time soon! Remember that Intel CPUs in computers on sale right now still have this bug.
Although one hopes and expects that AMD will be the immediate beneficiary of all this, I'd love to see the base of general purpose computing (i.e. PC) CPUs expanded to cover ARM and Power. Linux already runs on ARM and Power of course but to really open up the market as a whole Microsoft would need to port Windows to Power (and bring it back to ARM).
Footnote:-
1: CPU microcode updates are distributed through BIOS updates, and this could matter for Spectre on Intel and AMD CPUs.
Thanks. What exactly would the 2 flaws mentioned allow hackers to do? Would they just shut down your computer, or steal personal data?
The latter, access to data that they should not have access to.
It's not easy to exploit but it is exploitable and will be exploited.
One cannot help but wonder if the NSA, GCHQ, PLA, et al have known about this all along and are now gnashing their collective teeth that it's been found out. ;-)

I know precisely buggerall about all this, but it doesnt take much casual paranoia to imagine that the intelligence services have been aware of this for a while, and it has been the ultimate weapon in their armoury.
You could take it a step further, and speculate that its a deliberate back door incorporated into chip design by Big Tech, with or without collusion with governments. (And the whole we wont give up your privacy stand-off was just a smokescreen).
[Reaches for tinfoil hat, goes off to Conspiracy Theories thread]
Do we know who finally found these issues and disclosed them? Might give us a clue as to who knew beforehand and who didn't.
Well I got the gist.
Big flaw discovered with some chips in computers. Chance of attack and problems for your average person, low. Work ongoing to develop patches/updates to address problem. Allegedly the creators of said chips could face some sort of legal action and owners of affected devices could ask for a refund. But I think thats unlikely.
Best advice is to ensure you install updates and dont click on any dodgy websites and links.
Is that about right.
Best regards,
Ben

2 issues. One specific to Intel chips, being patched the other to do with the fundamental design flaws in ALL modern processors (albeit harder to exploit), also being 'patched' while not solving the actual issue.
Not clicking on dodgy websites / links is good practice full stop.
Never thought about the likes of GCHQ, NSA etc knowing (and er...exploiting backdoors this way) - interesting theory!!